- This article will enable you to communicate securely with your QNAP NAS server over the secure sockets layer protocol by utilising a purchased SSL Certificate.
- Please see the ‘Summary Overview’ tab below for a high level view of the objectives this ‘howto’ will achieve.
Why might I want to do this?
- To stop traffic from being read or copied by unknown parties on the internet.
- To help increase your search engine ranking with google.
- Because you don’t want to see the message SSL Certificate Not Trusted
- Because you don’t want to see the message SSL Certificate Error
To be clear, what does an SSL certificate do?
Simply put, an SSL (Secure Sockets Layer) certificate automates the process of verifying the encrypted information traveling between your web site and the web browser / application of the person viewing or using it. In the QNAP example, this could be a web site hosted on the NAS or between the QNAP NAS applications – (both apply in this howto).
You want to automate this process if you have a public facing web site that you wish to utilise SSL, or if you have many users that will connect to the NAS from the internet. Do note however, that a certificate is not necessary to do the actual encryption of your traffic, however, without a paid certificate, each user will either have to accept a security warning prompt upon initial setup or upon visiting your web site, or alternatively manually add a certificate that you provide in the form of a file. For this reason, it is usually much easier to use a paid certificate authority.
A word about security
Without a doubt, SSL is a very secure protocol employing 2048 bit encryption (optional 4096 bit) which is the only real security solution for web sites existing today. Until very recently, SSL had not been compromised. Through recent events brought to light from the Edward Snowden leaks, it turned out that the NSA had indeed compromised SSL. It is not yet known how this happened, except that it was very suspicious that a National Security Agency employee was co-chairing the very influential cryptography panel that creates these standards for the internet engineering task force (IETF). Keeping to topic, no encryption standard (be it DVD, Blu Ray, Sky TV, the Enigma code or SSL) has remained unbreakable forever and this is a natural part of the encryption lifecycle. SSL was developed in 1993 with the first publicly secure protocol available in 1996, so it’s a testament to the protocol to still be in use today.
Please note: If you’re using the web site for your own private uses, it is obvious that it can actually be more secure using the above mentioned, self signed certificate since there is no certificate authority knowing part of your SSL key. This was finally acknowledged during the Edward Snowden leaks and is known to be part of the way the NSA were able to break SSL. Obviously, this would be no good for an ecommerce site as your customers would be presented with a warning that you’re an untrusted web site and are unlikely to hand over their money.
Do you REALLY want to self host your own web site?
Ultimately, this web site and other things I’m working on have now been moved away from the QNAP NAS server for various reasons, including that the development team at QNAP simply don’t update their code enough for me to consider it really safe and secure. Other challenges with a self hosted site you might like to consider include: automating your own backup plan, redundancy of hardware in a failure, redundancy of internet connection, fail over during failure (DR), how much effort you put into your rebuild procedures (known as as-builts) and what that might mean for down time to your customers.
There isn’t much capability for BCP (Business Continuity Plan) with a public facing web site other than the above precautions, so before you go rushing off thinking a locally hosted web site is for you, consider how hard it may be to get things up and running again and how much down time for your customers that may end up resulting in, if you can’t bring your site up quickly. In my case with a fairly decent knowledge of IT, I could still find an outage causes days of downtime. For example: if an outage happens while I’m at my day job, it could be 8 hours before I could even start resolution steps and could require a very long night to complete. If it were failed hardware, it may even be unavailable for weeks while replacement parts arrive from overseas agents. And these cases are if you’re good at what you do, or lucky. In reality, things may take much longer and cost you much more money than a good hosting plan.
A word about hosting
These days you can get some pretty sweet deals on web site hosting that take much of the pain away for you. One I’ve recently discovered is Site5. US$4.95 per month get’s you Apache, mysql, unlimited disk space and unlimited traffic. I doubt that will be easy to beat. That said, there seem to be dozens of these shared infrastructure sites now available if you’re prepared to search. Have a look around and consider your options carefully. See our review of the ‘real’ price these hosting companies charge here.
SSL Certificate types
Something else to know about before you start is there are most definitely a number of different grades of SSL certificates available. On top of that there are differing brands of SSL certificates that each have their own types and certain brands may be trusted more than others. I won’t go into brands here, but when you sign up at a certificate authority, they should explain all this to you, so choose carefully for your use type.
The two things you need to know when choosing a certificate type are:
- What host or hosts (signified by domain names) will I need to protect?
- What kind of validation will I require?
So for point 1, will you be securing www.yourdomain.com, host1.yourdomain.com, mail.yourdomain.com etc, or just one of those?
For point 2, you can choose a higher grade of validation where the certificate authority will phone around and confirm that you are legitimate. It takes up to several weeks in some cases but apart from being the most expensive, this type will present a ‘green seal’ of approval in your customers browser which stands out like a sore thumb (in a positive way). It has quickly become the golden standard associated with secure browsing.
You can see at the below link, a list of different SSL types from Ssl’s.com which turns out to offer some of the most value in terms of SSL certs on the web. For a single host as low as $4.99 per year. Yes you read that right.
Software Dependencies
- SSL Certificate
- A fixed IP address or Dynamic DNS
Hardware Dependencies
- QNAP NAS Server
- An internet Modem / Router capable of performing
Tools Required
- SSH access
- A recent web browser
Other Dependencies
- A working internet connection
The below lists the high level summary of steps we’re about to take during this howto.
- Create a CSR (Certificate Signing Request)
- Upload the certificate code to SSL provider
- Apply the certificate to the QNAP NAS Server
- Configure the QNAP ports so the the certificate and system admin work together
- Configure the QNAP virtual hosts section
Purchase your certificate
Step 1a – Create your CSR (Certificate Signing Request)
This will generate a code from your NAS server that can be used to ‘unlock’ the partner code from the certificate authority.
Essentially what this does, is create a private key (private as in only your web site knows about it) and a matching CSR that you upload to your SSL provider, which in turn then allocates you a public key and an intermediate key. We’ll be doing this via SSLs.com, but this should map to any chosen provider.https://support.comodo.com/index.php?/Knowledgebase/Article/View/1/19/csr-generation-using-openssl-apache-wmod_ssl-nginx-os-x
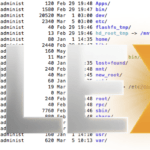
- Log in to an ssh terminal on your QNAP nas as admin.
- Create a new easily accessible directory somewhere on your NAS and call is SSL if you like.
- While in that directory, enter the following command: openssl req -nodes -newkey rsa:2048 -keyout your_domain_com.key -out your_domain_com.csr
You will be presented with a bunch of questions which can be a little tricky to understand at first, so we’ll summarise them here.
Country Name (2 letter code) [AU]: NZ State or Province Name (full name) [Some-State]: NorthIsland Locality Name (eg, city) []: Auckland Organization Name (eg, company) [Internet Widgits Pty Ltd]: YourCompany or WebSite Name Organizational Unit Name (eg, section) []: IT Common Name (eg, YOUR name) []: mysubdomain.mydomain.com Email Address []: hostmaster@yourdomain Also a challenge password is normally chosen which you will need to write down somewhere. I'm told this isn't actually needed for web sites, but I do it anyway.
**Remember the above command MUST be run in a session on the NAS, do not get confused if you have a Mac and run it locally on your Mac. It is OK to connect to the ssh terminal on your NAS via the mac though. So you’re going to need to do something like: ssh admin@yournasIP and then enter in your admin password first. If you have windows, you’ll need to download Putty and do it in there.
OK so at this point you have your generated csr and private key in your chosen directory, well done!
Step 1b – Upload to SSL’s.com
This uploads the codes you just generated to your SSL certificate provider
What I do here in Mac is type ‘cat mydomain.csr’ in windows you will need to use a text viewer or something. Copy and paste that with your mouse and upload it to your SSL page for the certificate you just purchased.
SSL’s will ask you for some additional information such as what email address you want it sent to and then you wait for it to arrive.
When the email arrives you will get similar to the following files in a zip file.
Attached to this email you should find a .zip file containing:
- Root CA Certificate – AddTrustExternalCARoot.crt
- Intermediate CA Certificate – COMODORSAAddTrustCA.crt
- Intermediate CA Certificate – COMODORSADomainValidationSecureServerCA.crt
- Your PositiveSSL Certificate – yourdomain_com.crt
Step 1c – Apply your certificate files to the QNAP
Using the same copy and paste method above (using cat or a similar text viewer) copy these to the NAS. You’ll want to paste them into the Security section, Certificate & Private Key tab as per the table below
COMODORSAAddTrustCA.crt goes into Intermediate Certificate Section
yourdomain_com.crt goes into Certificate Section
and the private key you generated earlier goes into the Private Key section.
That’s it! Well sort of – there are some other general items you need to be aware of before it will actually work.
Make it work with your system
Step 2a – Configure your NAS’s ports
There is actually likely to be a port conflict between your new web site and the admin page of the NAS. To get around this, you need to change the port your admin page uses.
Go to General Settings, System Administration
Change System port to 8080 and if you’re using SSL for the admin page, change that to 8081.
**Note, after this change you will need to do a few more things. Each time you access your admin page you will need to put :8080 or :8081 after your browser URL. So e.g. https://younasIPordomain:8081
In addition, if you use any of the QNAP phone apps, these will also have to have this port manually specified in the app.
If you use any of these apps over the internet, you will also now have to forward these ports in your router’s NAT to your NAS server or they won’t work.
OK, now that’s done, go to applications Web Server.
Ensure that your web server is set to use port 80 (even though you’ve done SSL, there are times when you need good old port 80 open. You don’t have to, it’s your choice.
Here, ensure the HTTPS port is set to 443. Obviously your router has to be set up to forward this too.
Step 2b – Configure your NAS’s Virtual Hosts
If you’re using virtual hosts, this is very simple, the format is:
Host Name: your domain name e.g. www.yourdomain.com
Folder Name: the folder where your entire web site is
Protocol: the HTTP or HTTPS protocol you’re setting up
Port: 80 if you chose HTTP above, or 443 if you chose HTTPS above.
I successfully had all this working with SSL and a virtual host as a wordpress blog on my QNAP, it has now however been moved to a hosting company as I needed something better.
One thing I noticed was on my first attempt the QNAP had a glitch and for some reason broke access to all my hosted web sites. What I found was that the QNAP had simply disabled the virtual hosts and in addition reset the port changes described above back to their defaults. If this happens, you can go back through this guide and double check the steps from 2a. Once I put it all back again I was up and running as per normal.
As always, I welcome your insights and opinions in the comments section below.
**Hosting a web site? Why not apply and follow our article on how to speed it up with a CDN here!
Marshalleq