**This is a legacy article which does not meet some of our quality standards. While it may contain useful information, is retained here for legacy reasons only.
There are different ways to set up Fortinet port forwarding, (using a DMZ for example), this article covers off the most basic example and can be applied to a DMZ setup later.
- Create a VIP first
- Go to firewall objects tab, virtual IP / Virtual IP
- Click create new
- Name: <Name of server you’re forwarding to>
- External Interface <Your external interface (in my case Chorus UFB)
- Type Static NAT
- External IP / Address Range: The IP address of your WAN supplied by your ISP (In both boxes if you only have one IP)
- Mapped IP / Address Range: The internal address of the server you’re forwarding to in the first box (the second box should auto populate).
- Port Forwarding: Leave unticked
- Second create a policy in your firewall
- On the policy tab, choose policy / policy
- Click Create New
- Source Interface / Zone (Your WAN connection) in my case Chorus UFB
- Source Address All
- Destination Address: <The Name you just gave your VIP connection>
- Schedule Always
- Service: Any single or multiple service that you wish to be forwarded to this IP address internally.
- You must enable NAT (although fortinet says you shouldn’t but I can’t get it to work otherwise).
- Do enable any logs, utm, shaping etc as you wish. (suggest a specific UTM profile for the specific ports that are opened in order to improve performance i.e. protect web, protect ssh etc.s
From the fortinet support page:
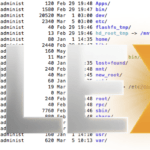
Test destination NAT by browsing to http://172.20.120.14 from the Internet. The session passes through the FortiGate unit to the web server which sends a response. Use the following packet sniffer command to see the results.
diagnose sniffer packet any ‘port 80’ 4 4
interfaces=[any]
filters=[port 80]
6.150356 wan1 in 172.20.120.12.51439 -> 172.20.120.14.80: syn 15893888
6.150637 internal out 172.20.120.12.51439 -> 192.168.1.110.80: syn 15893888
6.150803 internal in 192.168.1.110.80 -> 172.20.120.12.51439: syn 553485227 ack 15893889
6.150974 wan1 out 172.20.120.14.80 -> 172.20.120.12.51439: syn 553485227 ack 15893889
The first output line shows a packet from a client device with IP address 172.20.120.12 was received by the wan1 interface with destination address 172.20.120.14 and destination port 80.
The second output line shows that when the packet exits the internal interface the destination address is changed to 192.168.1.110 and the destination port is still 80.
The third output line shows the response from the web server.
The fourth output line shows the response from the web server being returned to the client device. The source address has been changed back to 172.20.120.14.
In this example, the source port is not changed.
Go to Policy > Policy > Policy and check the Count column for the security policy you added to verify that it is processing traffic.
Go to Policy > Monitor > Session Monitor to view the sessions being processed by the FortiGate unit. You can also see results by going to Policy > Monitor > Policy Monitor to view a graph of active sessions for each policy. Since there is only one policy, that graph contains only one entry. You can select the bar graph for the policy to view the top sessions by source address, destination address, or destination port/service.
The Top Sessions dashboard widget presents another view of sessions that you can also drill down into to get more info about current sessions. Other dashboard widgets display session history, traffic history, and per-IP bandwidth usage.